Stark Tech Provides Energy Solutions for the Total Optimization of Commercial & Industrial, Sustainable, and Critical Environments

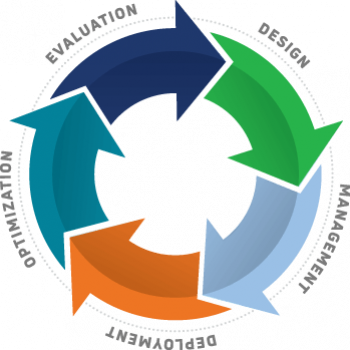
Turnkey implementation, master systems integration, equipment, and facilities management.


Turnkey design and build for comprehensive cleanroom and critical applications and equipment.
Diverse Energy Solutions for Enhanced Efficiency, Sustainability, & Cost Savings for Every Environment
Turnkey Project Management

End-to-End support from concept and design through project management & commissioning to scope and budget.
Building Technologies

Master Systems Integration with live monitoring & automated controls, actionable insights & optimization strategies.
BUILDING INTELLIGENCE

Command center live monitoring, strategic action and service that minimize operational disruptions and optimize performance.
Facilities Equipment

Engineered solutions for HVAC, critical power, and boiler and combustion applications to control temperature, humidity, IAQ
Parts & Service

Factory-trained & certified OEM service provider, including start-up, configuration & inspection qualification.
BATTERY ENERGY STORAGE

Battery energy storage systems and engineering support for large-scale deployments and microgrid applications.
Renewable Integrations

Clean-tech solutions for national accounts, including solar consulting, energy master planning, and implementation.
RNG & Compression

High-quality skid systems with engineering for compressed air, liquid applications, landfill, biogas & wastewater treatment.
In a quick 16-week turnaround, Stark Tech was able to install dehumidifiers to maintain tight humidity control in order to achieve the cleanroom conditions needed to convert the 306,000 sq. ft. warehouse into a mass production site.
In a green architecture design, Stark Tech incorporated a vegetated lower roof and photovoltaic collector on the upper roof with integrated temperature and lighting controls to maintain parameters that save energy and cost.
The project is a 350 scfm waste water treatment plant. “The ability to capture biogas from our sewage (and transform it into RNG) is the type of innovative project that will help us reach our renewable energy goals sooner rather than later.
Connect with a Stark Rep Today
Copyright © 2024 | All Rights Reserved
request a quote
By requesting a quote for sustainable initiatives in energy efficiency, you gain access to tailored expert knowledge and guidance. Discover innovative technologies and cost-saving measures promptly, empowering you to make informed choices and take control of your energy efficiency goals.